Malicious software on Windows systems can alter core processes, disrupt normal operation, and expose sensitive data without immediate visibility to the user. Infections often embed themselves within startup routines, background services, or system files, allowing them to persist even after basic removal attempts. Addressing these threats requires a methodical approach that examines system behavior, identifies unauthorized processes, and traces how the infection interacts with the operating environment.
Effective removal focuses on isolating and eliminating malicious components while preserving the integrity of legitimate system functions. This involves resolving hidden persistence mechanisms, restoring altered configurations, and ensuring that no residual activity remains that could reintroduce the threat. The objective is to return the system to a stable and secure state, where performance, reliability, and data integrity are no longer compromised by unwanted software.
Why Clients Trust Our Virus and Malware Removal Service
We take a thorough, methodical approach to system cleanup and security.
- Experienced Technicians skilled in identifying complex malware threats
- Efficient Service for infected or unstable Windows systems
- Thorough System Analysis to uncover hidden infections
- Transparent Pricing with clear explanations
- Service Warranty for added confidence
- Local Support in Miami serving Miami-Dade County
How the Virus Removal Process Works
- System Evaluation – Your Windows computer is inspected for active threats
- Threat Analysis and Quote – We explain what’s infected and how it will be resolved
- Complete Cleanup and Protection Setup – Malware is removed and safeguards applied
- Final Testing – System performance and stability are verified
System Integrity Restoration and Post-Removal Verification
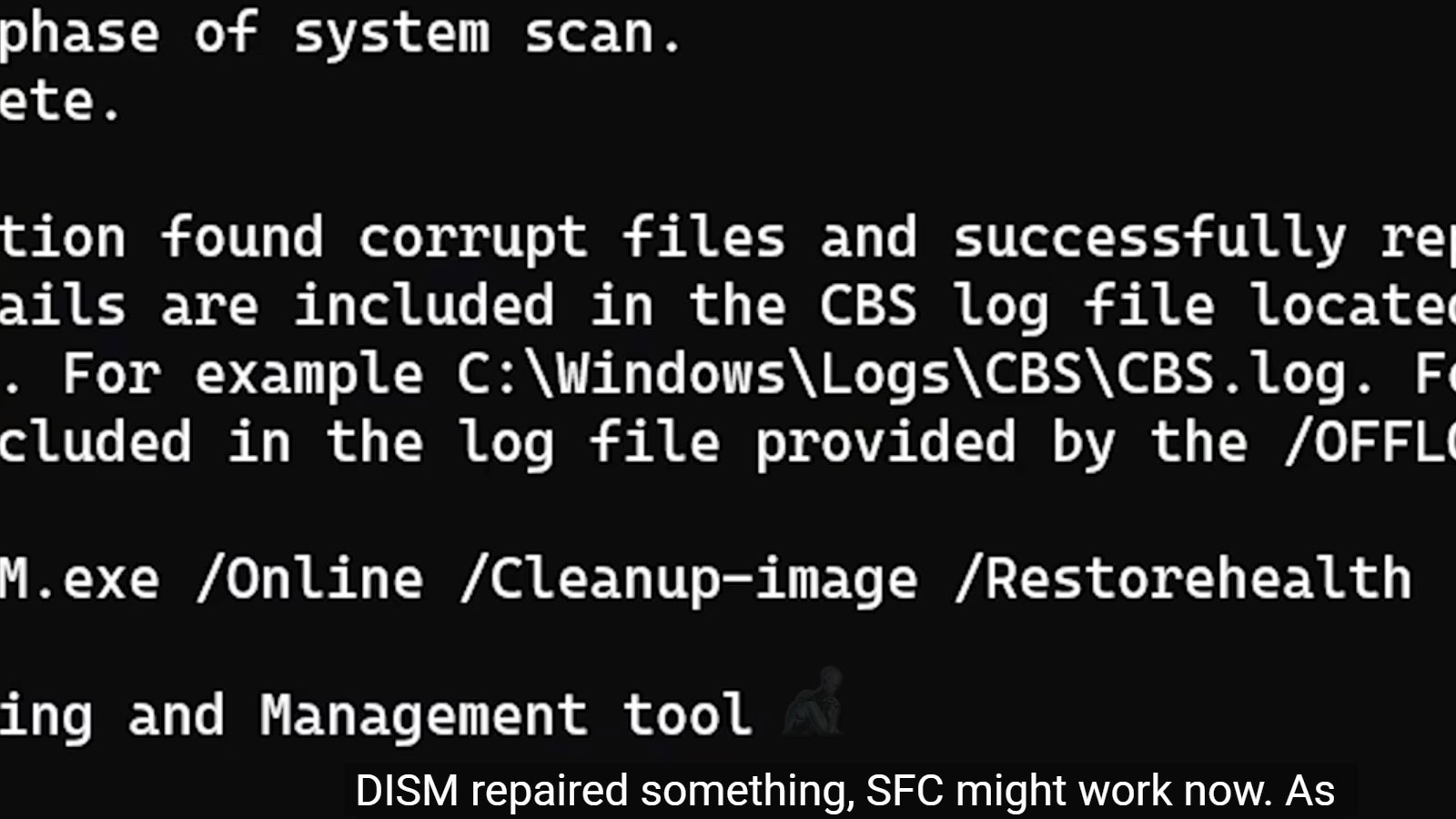
Removing malicious software is only one part of the recovery process. In many cases, infections leave behind changes that affect system stability, performance, or configuration. These can include altered permissions, damaged system files, or disrupted network settings that continue to impact the system even after the threat has been eliminated.
Verification focuses on confirming that the operating environment has been fully restored to a consistent and secure state. This includes ensuring that core system functions operate correctly, background processes behave as expected, and no residual anomalies remain. A thorough validation phase ensures that the system is not only free of threats but also capable of maintaining stable performance moving forward.
Common Virus and Malware Issues We Resolve
- Slow performance and frequent system freezing
- Persistent pop-ups, browser redirects, or hijacked homepages
- Unknown background processes or suspicious software
- Ransomware infections and locked files
- Spyware, keyloggers, and credential-stealing threats
- Trojan infections and malicious startup programs
Windows Malware Cleanup and System Protection
Our cleanup process is designed specifically for Windows-based computers to ensure stability and security after the infection is removed.
- Deep virus and malware scanning to eliminate hidden threats
- Spyware and adware removal to restore normal behavior
- Ransomware containment and recovery support when possible
- Antivirus and security software configuration
- Firewall and network security checks
- Data safety verification to prevent file corruption or loss
Persistence Mechanisms and Hidden Threat Behavior
Many forms of malware are designed to remain active even after partial removal, using persistence techniques that allow them to reload during system startup or operate silently in the background. These mechanisms can include modified registry entries, scheduled tasks, injected processes, or alterations to system services that are not immediately visible through standard inspection. As a result, infections may appear resolved while still maintaining a foothold within the operating system.
Understanding how these threats maintain presence is essential for complete removal. Identifying persistence points requires careful examination of startup behavior, background activity, and system-level modifications that deviate from normal operation. Addressing these hidden elements ensures that the infection is fully eliminated rather than temporarily suppressed, reducing the risk of recurrence.
Malware and viruses don’t just slow systems down, they put data and privacy at risk. With proper cleanup and protection, your windows computer can return to stable, secure operation. If your system is showing signs of infection, professional removal can make a real difference. Service Area: Miami and Miami-Dade County. Clean systems. Stable performance. Secure computing.